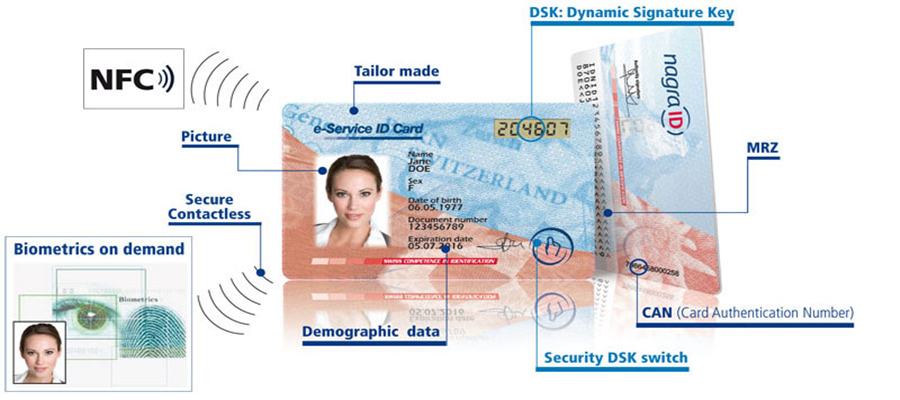
Smart card-enabled applications are becoming more prevalent in many of today’s businesses. Because cryptography operations are isolated from the operating system, secure smart card are not susceptible to attacks on the operating system, such as buffer overflow attacks and memory dump attacks,which might reveal private keys or other cryptography secrets. The secure smart card is protected from misuse by the PIN, which is known only to the smart card’s owner.
Because logon credentials accompany the user, you can issue a single secure smart card to each network user to provide a single set of logon credentials for logging on to local and remote networks, which can reduce the cost of administering separate user accounts for logging on to a network and logging on remotely. Furthermore, because the administrative support that is required to manage user passwords is a significant cost for most large organizations, you can deploy smart cards to reduce the cost of supporting users who forget their passwords or let their passwords expire. Mobile phones are widely used in Europe, so smart cards have become very common.
To use the secure smart card, the user inserts the card in a CXJ smart card reader that is attached to a computer and, when prompted, enters the PIN. The smart card can be used only by someone who possesses the smart card and knows the PIN. In addition, dictionary attacks or brute-force attacks can be attempted only by someone in physical possession of the card. However, even when an attacker has the card in his or her possession, the smart card locks after only a few failed attempts by the attacker to guess the PIN. So dictionary attacks and brute-force attacks on smart cards are not feasible even then.
Another benefit of secure smart card is that policies for PIN can be less restrictive than policies for network passwords. Windows 2000 supports logging on with a smart card for the network logon process by using extensions to the Kerberos v5 protocol. For logging on to a network, users usually press CTRL+ALT+DEL to initiate the Windows 2000 secure logon sequence. Third-party vendors provide a variety of smart card applications that might meet your needs.
When the secure smart card logon process is enabled, a user inserts the smart card to initiate the windows 2000 secure logon sequence. If the user’s PIN and smart card credentials are valid, the user is logged on and granted rights and permissions for the user account. When an administrator enrolls for a smart card logon certificate on behalf of the user, Windows 2000 automatically maps the smart card certificate to the user’s account in Active Directory. Therefore, smart card certificates for logging on to the network must be issued by a trusted enterprise CA.