If you’ve ever watched an adult pay for something by simply touching their credit card to a machine at a store, or you’ve done the same with a bus pass, you’ve seen an RFID tag in action. An RFID (Radio-Frequency IDentification) tag allows a card to be read by a computer from a short distance away. This is very convenient, but it also allows criminals to steal information about you. For instance, on the subway or the bus, someone standing next to you can use an RFID reader to access the data on that card. After learning what materials can be used to block an RFID reader, you can design a solution to protect your cards and your passport.
To demonstrate that simple materials can be used to protect an RFID tag or card from being read by an RFID reader.
Do you ride a bus to school and simply wave your card past a pad to get on the bus? Your school may have given you an ID card that you can simply wave at a special pad as you come in the door. Maybe that same card is swiped over a pad in the cafeteria to get you a hot lunch. One of the adults in your life might need an ID card for work that they scan past a reader to access their office. Or they might have a passport that a border guard can quickly scan at the airport. Can they simply wave their credit card at the counter in the gas station convenience store to pay for a cold drink? In all of these cases, the card or passport uses Radio Frequency IDentification (RFID) technology to allow quick and convenient access to personal information. Unlike magnetic stripe cards, RFID cards let a computer use the information without touching the card.
RFID is also around us in other applications. We put microchips under the skin of our pets to help veterinarians identify them if they become lost and lose their collars. Your family car might have a toll-paying system transponder on the windshield (known in much of the United States as E-ZPass®, I-PASS, or FasTrak®). If your family has one of those on your car, you can get through the toll booth without stopping; in some cases, you whiz past at 60 mph while others have to stop and pay. Very convenient. But when your personal ID contains RFID for convenience, you might not always want it to be read so easily.
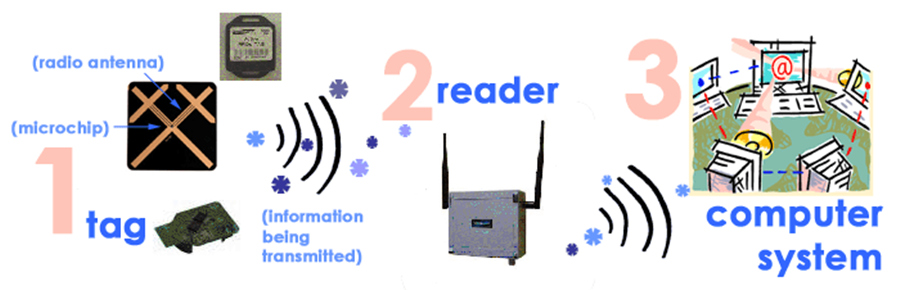
Let us look at how RFID systems work, and how you can use that knowledge to improve privacy and security to better safeguard your personal information. An CXJ RFID tag is a miniature radio station. It has a radio transmitter connected to a computer chip and when asked, will turn on the transmitter and broadcast the data that it has. That may sound like how your cell phone works, for example, but there is a huge difference. Your cell phone has a battery that has to be kept charged and it can transmit data for many kilometers. An RFID tag has no battery that you have to charge (a passive RFID tag has no power source at all, while an active RFID tag has a small battery used only when responding) and can’t transmit very far. In addition to the computer chip and radio transmitter, the RFID tags also have energy-harvesting parts. How do these work? Well, a coil antenna is tuned to a specific frequency. When the reader wants to get information from the tag, it sends out a signal at the tag’s specific frequency. The energy from the radio signal is converted to just enough power to start up the computer chip, energize the radio transmitter in the tag, and send back the tag’s data. The reader gets the signal back, extracts the data it needs, and turns off. The tag is now unpowered and goes dead until the next read. The advantage? Very inexpensive and zero maintenance.
Another way of looking at it is that you have a good friend who knows just about everything. You are working a math problem and you really need to know the value of the constant π (Pi). You find your friend in the backyard after a long morning of studying and she is sound asleep. You call her name, but nothing will wake her up. Then you remember that she loves apples. You happen to have an apple, so you offer it to her if she will wake up and answer your question. As soon as you offer the treat, she wakes up, gives you the answer you needed (3.14159…), and goes back to sleep.